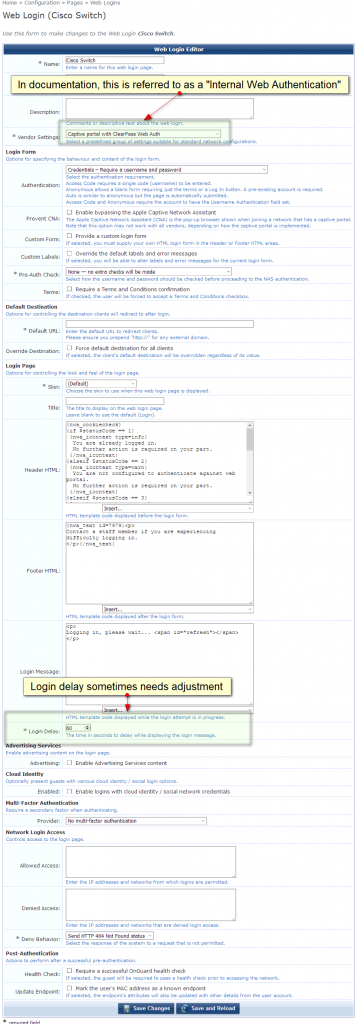
Here are some notes on getting a basic ClearPass Captive Portal page to authenticate an unknown wired client connected to a Cisco Catalyst 3560. Before this is all done, make sure the NAD has been added to ClearPass.
First.. the general algorithm
- Mac Auth Service – Allow all
- Radius Request
- Authenticaiont Success
- Radius url-redirect VSAs sent
- User Sends HTTP traffic
- User redirect to ClearPass Portal
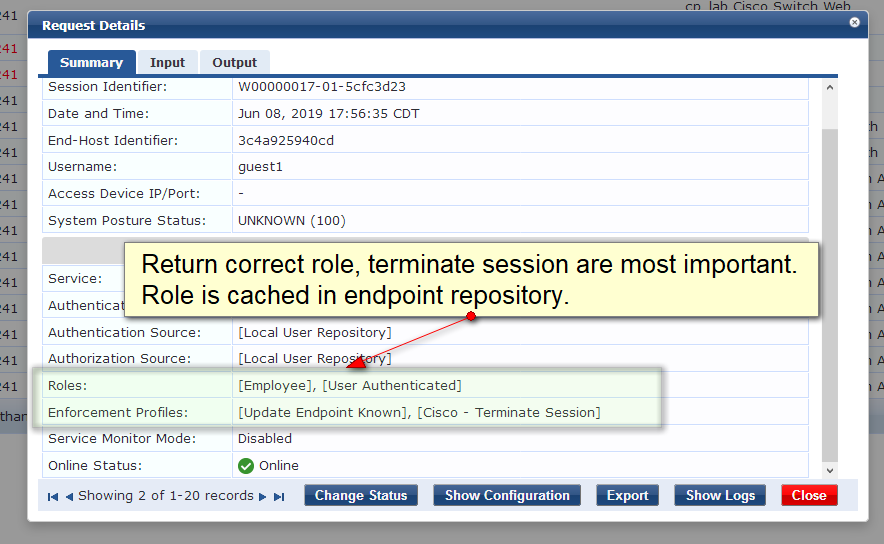
- User Sends Login from Portal
- Web Auth Occurs
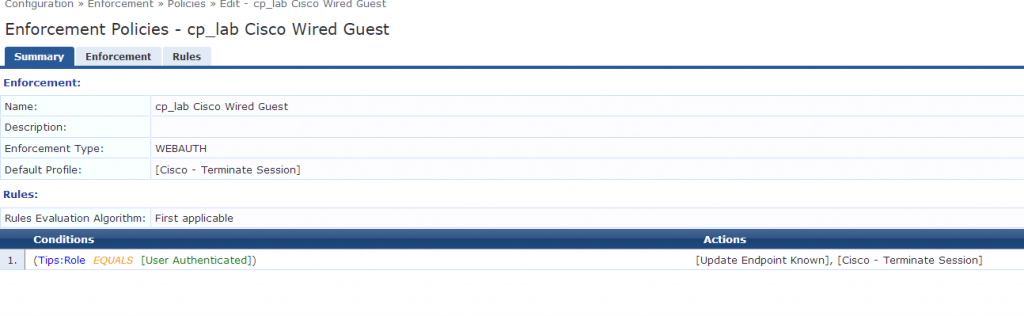
- On Success- Radius CoA Terminate Session
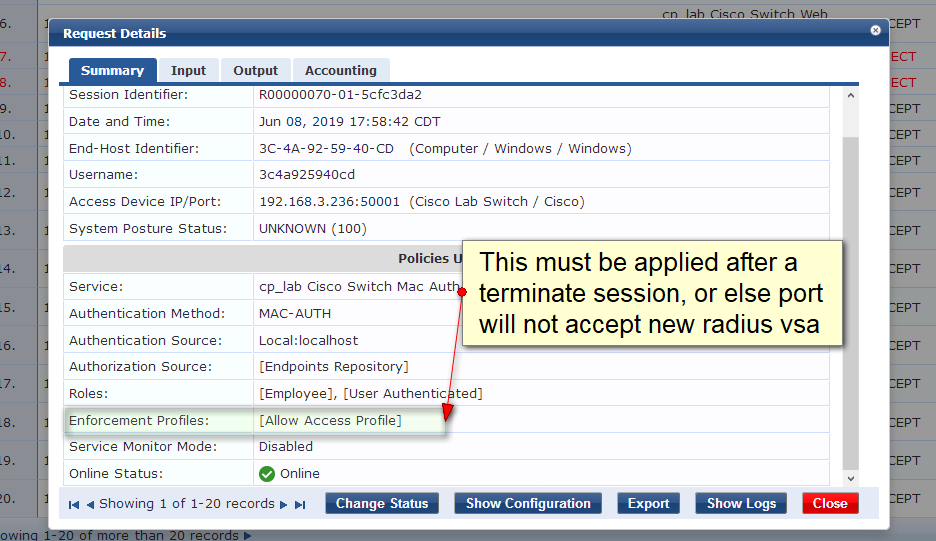
- MAC Auth Service – Reauthenticate
- Radius Allow All Access VSA Sent
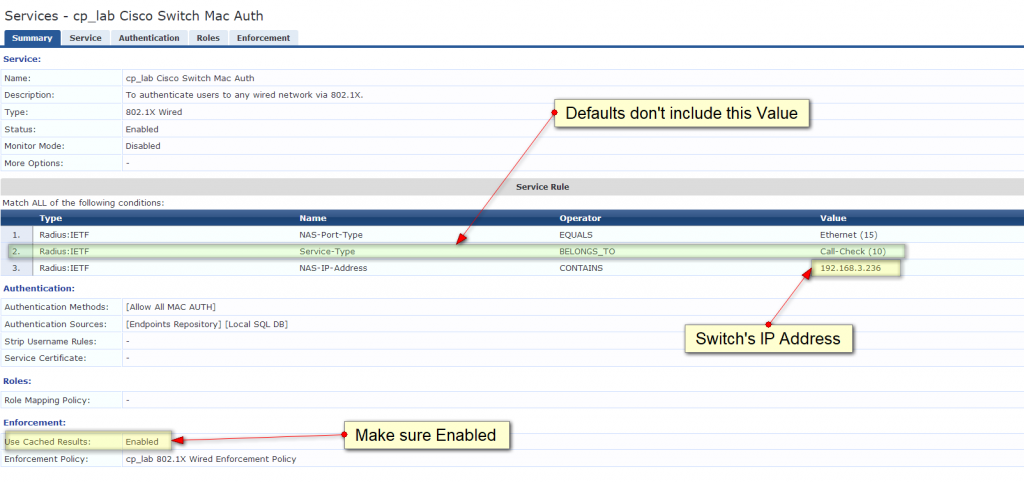
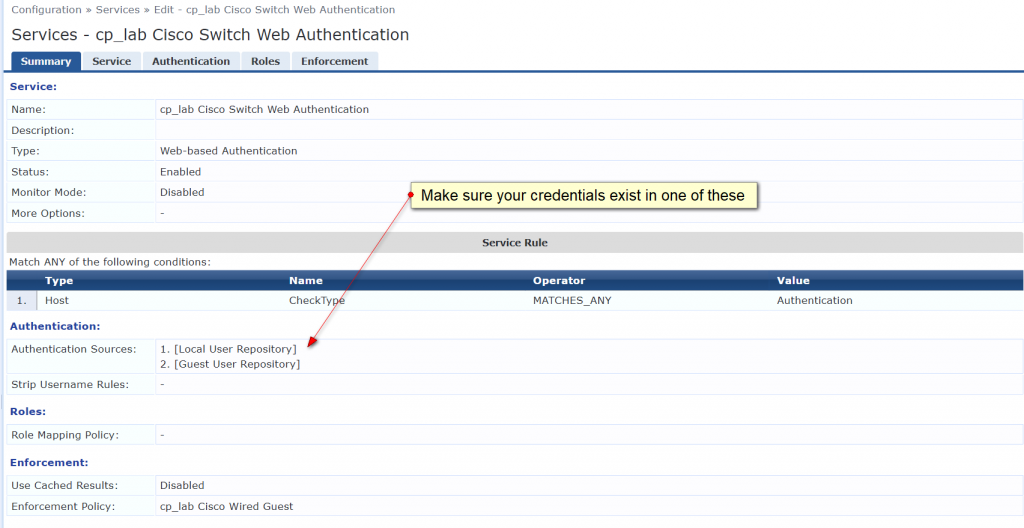
The first trick is to get the Wired Mac policy to classify. The default IETF attributes will not work, you must check access tracker for the correct inputs that are being sent from the authenticator (switch).
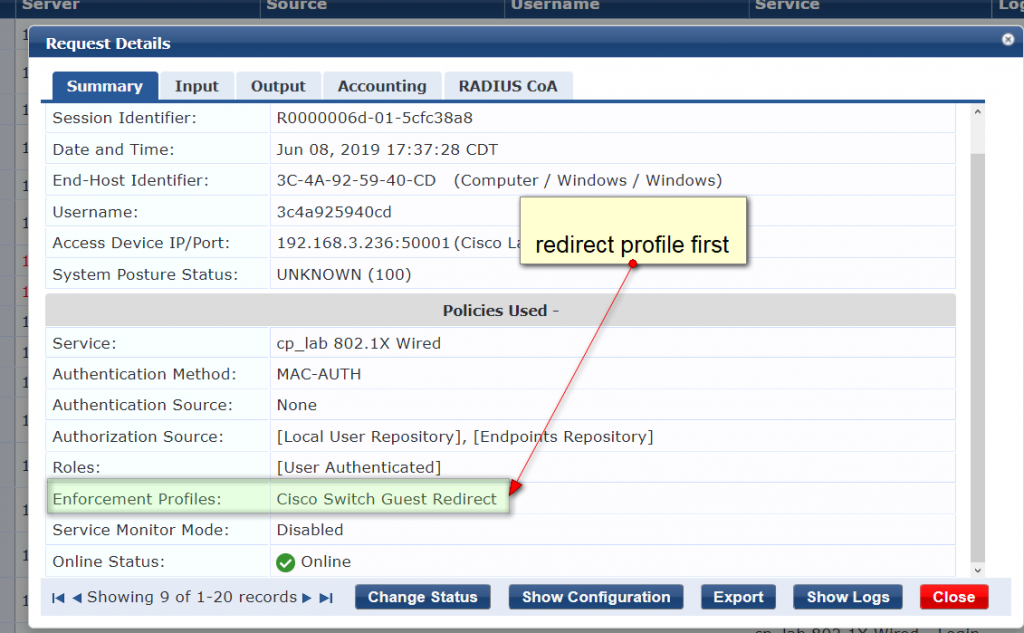
The second gotcha is the Use Cached Policy checkbox in the Enforcement tab. Its not really emphasized in the documentation, but after the web auth happens, the MAC caching policy will not pick up the role assigned unless you enable the cached policy check.
There are many pages on Aruba’s documentation sites that document the required switch configuration, the main configuration lines are the following:
aaa new-model
interface VlanXXX
ip address 192.168.X.XXX 255.255.255.0
ip helper-address <CP_IP>
dot1x system-auth-control
aaa authentication dot1x default group radius
aaa authorization network default group radius
aaa accounting update periodic 1
aaa accounting dot1x default start-stop group radius
aaa server radius dynamic-author
client <CP IP> server-key aruba123!
port 3799
auth-type all
ip dhcp snooping
ip device tracking
ip access-list extended weblogin
deny tcp any host 192.168.3.241
permit tcp any any
radius-server host <CP_IP> key <RADIUS_KEY>
interface FastEthernet0/1
switchport access vlan X
switchport mode access
authentication order dot1x mab
authentication priority dot1x mab
authentication port-control auto
authentication periodic
authentication timer reauthenticate server
mab
dot1x pae authenticator
dot1x timeout server-timeout 30
dot1x max-req 3
dot1x max-reauth-req 3
spanning-tree portfast
!
Other useful switch config hints:
# Make sure the native VLAN is set for the trunk port
interface GigabitEthernet0/1
switchport trunk encapsulation dot1q
switchport trunk native vlan X
switchport trunk allowed vlan X
switchport mode trunk
!
ntp server 216.239.35.0 prefer
clock timezone CST -5 0
clock summer-time CDT recurring
enable password cisco
!
username cisco privilege 15 password 0 cisco