When setting up the guest network between an IAP with ClearPass, the older guides direct the user to setup a PreAuth role for guest and deny all traffic.
It’s assumed a firewall exception or something similar is automatically put into the IAP firewall rules to let the IAP, client, and the ClearPass server communicate, but this isn’t the case currently. In addition to denying traffic to all servers, you need to add additional rules to let the client communicate with ClearPass AND the IAP – or else radius requests will fail.
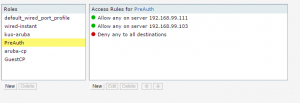
The PreAuth role looks similar to the following:
- 192.168.99.111 is the IAP’s Virtual Controller
- 192.168.99.103 is the ClearPass server